Programming Security - The Smart Contract Revolution
Part of "Exploring The Architecture of Trust Through Modern Wallet Design : From mathematical certainty to social consensus"
I’ve been running an experiment for the past month. Every morning, I check on a wallet that signs transactions while I sleep, pays for things I never explicitly approve, yet has never been compromised. The wallet enforces spending limits I configured months ago, automatically revokes permissions from applications I haven’t used recently, and would transfer my assets to predetermined beneficiaries if I stopped interacting with it for 90 days.
This isn’t science fiction. It’s an ERC-4337 smart contract wallet running on Ethereum, and it represents a fundamental shift in how we think about digital asset security. We’re no longer just protecting keys but programming security itself.
In Parts 1 and 2 of this series, we explored how HD wallets created a “beautiful prison” of determinism and how MPC distributed secrets without them ever existing. Smart contract wallets take a different approach entirely: instead of focusing on key management, they transform wallets into autonomous agents with programmable logic. The security isn’t in the key; it’s in the code.
The Account Abstraction Revolution
Let me start with a provocative question: Why should a wallet need a private key at all?
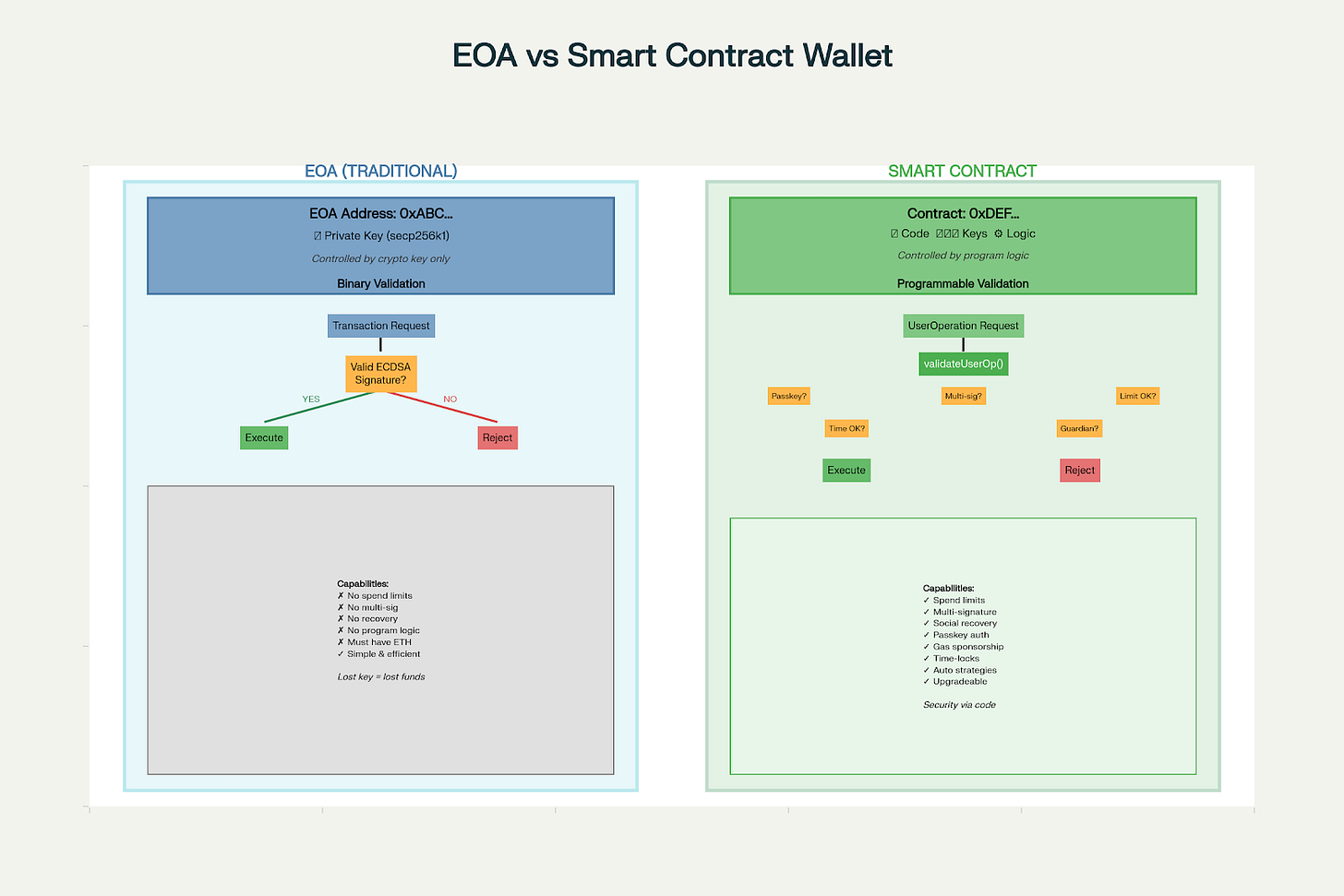
Traditional Ethereum accounts (EOAs) are simple: a private key controls an address. Every transaction must be signed with ECDSA on the secp256k1 curve. No exceptions, no flexibility, no programmability. It’s beautifully simple and frustratingly rigid.
def traditional_eoa_limitation():
“”“
EOAs are cryptographically pure but functionally primitive
“”“
# An EOA can only do one thing: sign with its private key
if has_private_key:
can_sign_transaction = True
else:
can_do_nothing = True
# No logic, no conditions, no flexibility
# Lost key = lost funds, always and forever
# No spending limits, no multi-sig, no recovery
# Just pure, unforgiving cryptographyERC-4337 shatters this constraint by introducing account abstraction and allowing smart contracts to act as wallets with arbitrary validation logic:
def smart_wallet_validation():
“”“
Smart contracts can validate transactions however they want
“”“
# The validateUserOp function becomes the wallet’s brain
def validateUserOp(userOp, userOpHash):
# Could check a passkey signature
if verify_passkey_signature(userOp.signature):
return VALID
# Could require multiple signatures
if count_valid_signatures(userOp.signature) >= 2:
return VALID
# Could check spending limits
if userOp.value < daily_limit:
return VALID
# Could require time delays for large amounts
if userOp.value > threshold and time_elapsed > delay:
return VALID
# The possibilities are literally endlessThis shift from “cryptographic authority” to “programmable authority” changes everything. Security becomes a design problem, not just a key management problem.
The UserOperation: Transactions Reimagined
The genius of ERC-4337 lies in the UserOperation - a new primitive that replaces traditional transactions for smart wallets:
def user_operation_anatomy():
“”“
UserOperations aren’t transactions; they’re intentions
“”“
userOp = {
‘sender’: ‘0x...’, # The smart wallet contract
‘nonce’: 0,
‘initCode’: ‘0x...’, # Deploy wallet if needed
‘callData’: ‘0x...’, # What to execute
‘callGasLimit’: 100000,
‘verificationGasLimit’: 50000,
‘preVerificationGas’: 21000,
‘maxFeePerGas’: 20,
‘maxPriorityFeePerGas’: 2,
‘paymasterAndData’: ‘0x...’, # WHO PAYS FOR GAS?
‘signature’: ‘0x...’ # Flexible validation
}
# The killer feature: paymasterAndData
# Someone else can pay for your transaction!
# This enables gasless onboarding - users don’t need ETH to startThe Paymaster concept is revolutionary. New users can interact with your application without first acquiring ETH for gas. Applications can sponsor user transactions, implement subscription models, or accept payment in any ERC-20 token. This solves one of crypto’s biggest UX problems: the gas fee chicken-and-egg.
Practical Security Patterns
Let me walk through actual smart wallet security patterns I’ve implemented or observed in production:
Pattern 1: Progressive Security
contract ProgressiveSecurityWallet {
uint256 constant SMALL_AMOUNT = 0.1 ether;
uint256 constant MEDIUM_AMOUNT = 1 ether;
uint256 constant LARGE_AMOUNT = 10 ether;
function validateTransaction(uint256 amount, bytes signatures) {
if (amount < SMALL_AMOUNT) {
// Single signature (phone passkey) sufficient
require(validatePasskey(signatures));
} else if (amount < MEDIUM_AMOUNT) {
// Require phone + hardware key
require(validatePasskey(signatures));
require(validateHardwareKey(signatures));
} else if (amount < LARGE_AMOUNT) {
// Add time delay
require(validateMultiSig(signatures, 2));
require(timeDelayElapsed(48 hours));
} else {
// Maximum security: 3-of-5 multi-sig + 1 week delay
require(validateMultiSig(signatures, 3));
require(timeDelayElapsed(7 days));
}
}
}This pattern acknowledges that not all transactions need maximum security. Buying coffee doesn’t need the same protection as transferring your life savings.
Pattern 2: Social Recovery
contract SocialRecoveryWallet {
address[] public guardians;
uint256 public recoveryThreshold = 2;
mapping(address => address) public proposedOwner;
mapping(address => uint256) public proposalVotes;
function initiateRecovery(address newOwner) external {
require(isGuardian(msg.sender));
proposedOwner[msg.sender] = newOwner;
proposalVotes[newOwner]++;
if (proposalVotes[newOwner] >= recoveryThreshold) {
// Transfer ownership after time delay
scheduleOwnershipTransfer(newOwner, 48 hours);
}
}
}Vitalik Buterin has long advocated for social recovery as the solution to key loss. Guardians can be friends, family, or institutions, basically anyone you trust to help recover your wallet but not collude to steal from you.
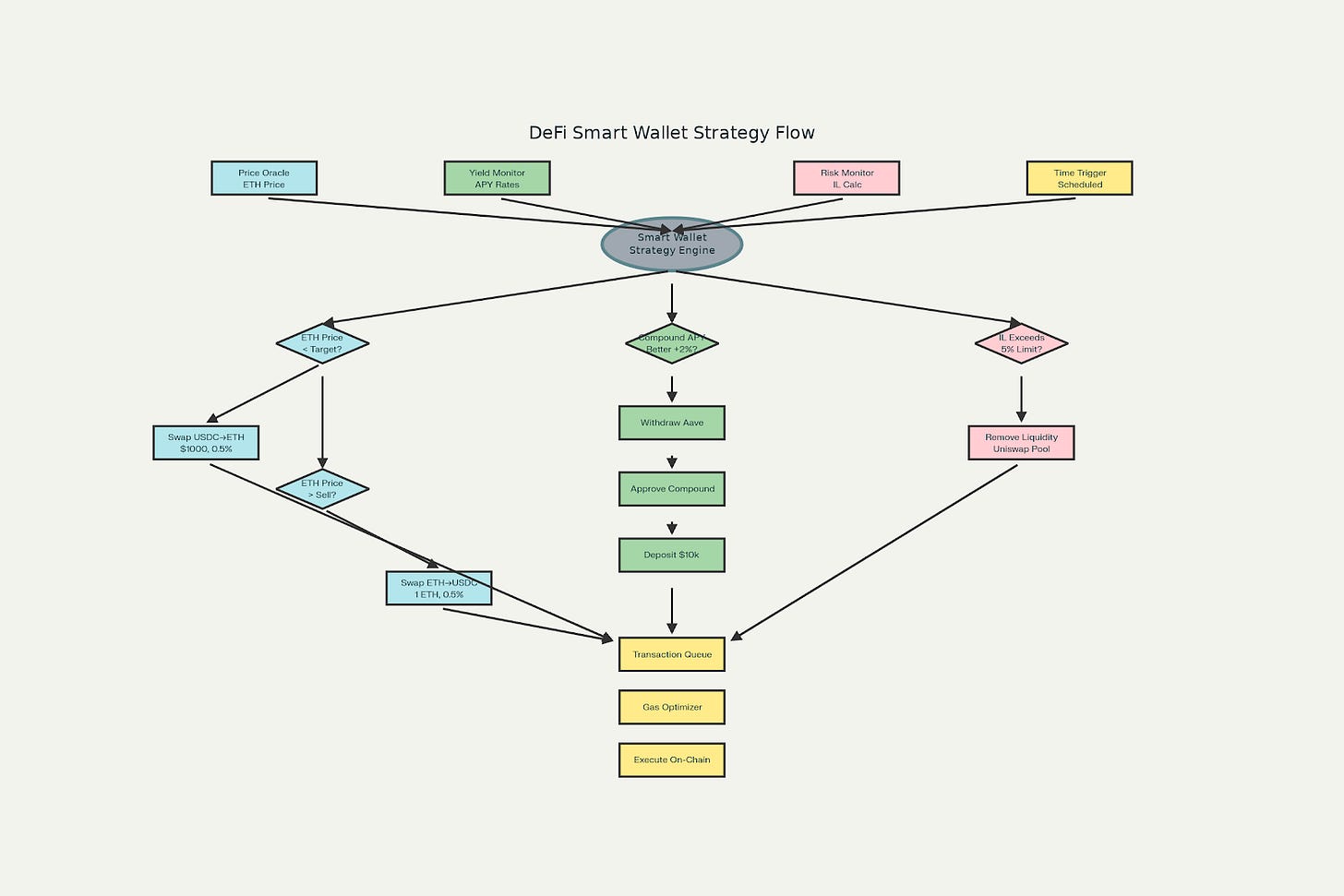
Pattern 3: Automated DeFi Strategies
def automated_defi_wallet():
“”“
Smart wallets can execute complex DeFi strategies autonomously
“”“
class DeFiWallet:
def executeStrategy(self):
# Check if conditions are met
if eth_price < target_buy_price:
# Auto-buy ETH with USDC
self.swap(USDC, ETH, amount)
if apy_compound > apy_aave + 2_percent:
# Move funds to better yield
self.withdraw(aave_pool)
self.deposit(compound_pool)
if impermanent_loss > threshold:
# Exit liquidity position
self.remove_liquidity(uniswap_pool)
# All without manual intervention!This isn’t just about security but about capability. Smart wallets can be programmed to act on your behalf, executing strategies while you sleep.
The Hidden Complexity
But here’s where things get complicated. I discovered this the hard way when deploying a smart wallet for a client:
def deployment_cost_reality():
“”“
Smart wallets aren’t free and deployment costs are real
“”“
# Deploying a smart wallet contract
deployment_gas = 300_000 # Conservative estimate
gas_price = 30 gwei # Current Ethereum mainnet
eth_price = 3000 # USD
deployment_cost_usd = (deployment_gas * gas_price * eth_price) / 10**9
# Result: ~$27 per wallet
# For 1000 users: $27,000 in deployment costs!
# Solution: Counterfactual deployment
# Wallet address exists before deployment
# Only deploy when first transaction occursThis led me to discover counterfactual deployment, i.e., wallets that exist in potential but not reality. The address is deterministic (computed from CREATE2), but the contract only deploys when needed. Users can receive funds at their wallet address before the wallet exists!
The Bundler Economy
One of the most fascinating aspects of ERC-4337 is the emergence of bundlers - specialized nodes that aggregate UserOperations:
def bundler_economics():
“”“
Bundlers are like Uber for transactions
“”“
class Bundler:
def collect_user_ops(self):
# Gather UserOperations from mempool
ops = self.mempool.get_pending_ops()
# Simulate each one (costs computational resources)
valid_ops = []
for op in ops:
if self.simulate(op).is_valid:
valid_ops.append(op)
# Bundle and submit
bundle = self.create_bundle(valid_ops)
tx_hash = self.submit_to_chain(bundle)
# Collect fees from each UserOp
# This is a competitive market!Bundlers compete on efficiency, reliability, and fee structures. It’s a new economy emerging within Ethereum; a class of infrastructure providers who never hold user funds but are essential for smart wallet operations.
Attack Vectors and Mitigations
Smart contracts introduce new attack surfaces that don’t exist in traditional wallets:
The Signature Replay Attack
// VULNERABLE CODE
function execute(address to, uint256 value, bytes data, bytes signature) {
bytes32 hash = keccak256(abi.encodePacked(to, value, data));
require(isValidSignature(hash, signature));
// DANGER: No nonce! Signature can be replayed!
(bool success,) = to.call{value: value}(data);
}
// SECURE CODE
function execute(address to, uint256 value, bytes data, uint256 nonce, bytes signature) {
require(nonce == currentNonce++);
bytes32 hash = keccak256(abi.encodePacked(to, value, data, nonce, chainId));
require(isValidSignature(hash, signature));
// Safe: Includes nonce and chainId
(bool success,) = to.call{value: value}(data);
}The Module Security Problem
def module_security_analysis():
“”“
Modular wallets can install new capabilities - but this is dangerous
“”“
# ERC-7579 enables modular smart accounts
# Wallets can install validators, executors, hooks
# The risk: Malicious modules
class MaliciousModule:
def onInstall(self, wallet):
# Looks innocent
self.wallet = wallet
def onExecute(self):
# But contains backdoor
if self.trigger_condition():
self.wallet.transfer(attacker, all_funds)
# Mitigation: Module registries and audits
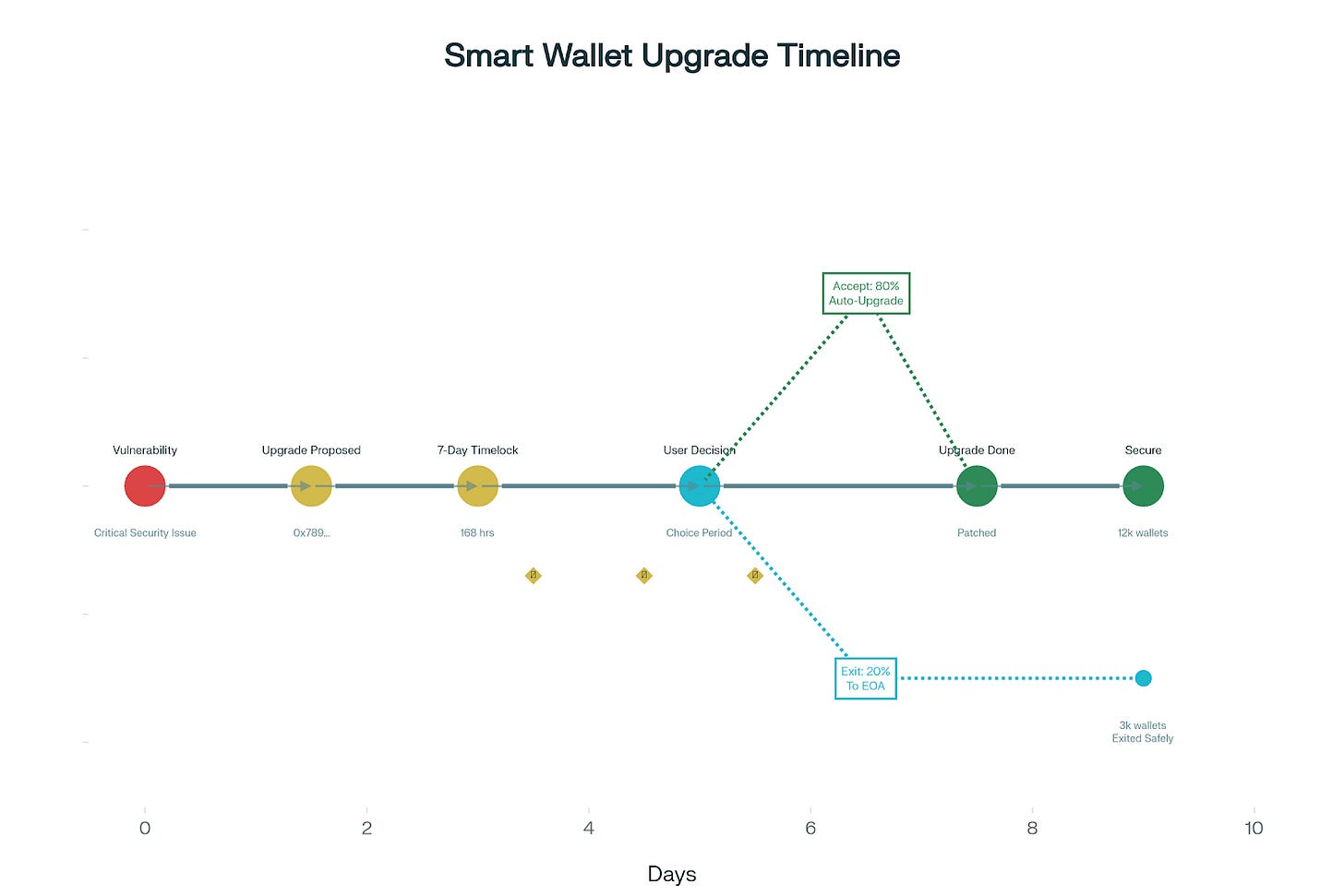
# But who watches the watchers?The Upgrade Dilemma
One of the most contentious aspects of smart wallets is upgradeability:
contract UpgradeableWallet {
// The dilemma: Fix bugs vs. introduce new ones
function upgrade(address newImplementation) external onlyOwner {
// Owner can upgrade wallet logic
// Pro: Can fix vulnerabilities
// Con: Can introduce backdoors
_setImplementation(newImplementation);
}
// Alternative: Time-locked upgrades
function proposeUpgrade(address newImplementation) external onlyOwner {
upgradeProposal = newImplementation;
upgradeTime = block.timestamp + 7 days;
emit UpgradeProposed(newImplementation, upgradeTime);
// Users have 7 days to exit if they disagree
}
}This creates a philosophical question: Is a wallet that can be upgraded truly non-custodial? If the wallet provider can push updates, do you really control your assets?
Cross-Chain Complications
Smart wallets reveal the complexity of cross-chain operations:
def cross_chain_challenges():
“”“
Same wallet, different chains, different addresses?
“”“
# Problem: Contract addresses depend on deployment
ethereum_wallet = “0x123...” # Deployed at nonce 5
polygon_wallet = “0x456...” # Different address!
# Users confused: “Why are my addresses different?”
# Solution: CREATE2 deterministic deployment
salt = user_passkey_hash
init_code = wallet_bytecode
# Same address on all chains!
address = create2_address(factory, salt, init_code)
# But wait: Different factory addresses per chain?
# The complexity never ends...The Gas Abstraction Revolution
Perhaps the most user-friendly innovation is gas abstraction through Paymasters:
def paymaster_patterns():
“”“
Paymasters enable business models impossible with EOAs
“”“
class SubscriptionPaymaster:
def validatePaymasterUserOp(self, userOp):
# Check if user has active subscription
if self.subscriptions[userOp.sender].active:
return SPONSORED
class TokenPaymaster:
def validatePaymasterUserOp(self, userOp):
# Let users pay gas in USDC instead of ETH
usdc_amount = calculate_gas_in_usdc(userOp)
if check_user_balance(userOp.sender, usdc_amount):
return ACCEPT_USDC_PAYMENT
class ConditionalPaymaster:
def validatePaymasterUserOp(self, userOp):
# Sponsor only specific operations
if is_nft_mint(userOp.callData):
return SPONSOR_NFT_MINTS
if is_first_transaction(userOp.sender):
return SPONSOR_ONBOARDINGThis enables Web2-like business models: freemium services, subscriptions, loyalty programs. Users don’t need to understand gas since applications handle it invisibly.
The Censorship Resistance Question
A concerning aspect of ERC-4337 is the bundler dependency:
def censorship_analysis():
“”“
Bundlers introduce potential censorship vectors
“”“
# Traditional EOAs: Submit directly to mempool
# Smart wallets: Must go through bundlers
# What if bundlers refuse your UserOps?
scenarios = {
‘regulatory_pressure’: ‘Bundlers block sanctioned addresses’,
‘competitive_censorship’: ‘Bundlers favor certain protocols’,
‘economic_censorship’: ‘Only high-fee operations processed’,
‘ideological_censorship’: ‘Bundlers refuse certain dApps’
}
# Mitigation: Decentralized bundler network
# But currently, most bundlers are centralized services
# This is an unsolved problemThe ERC-4337 community is working on a shared mempool for UserOperations, but centralization risks remain real.
Comparing Security Models
Let’s examine how smart wallets compare to our previous approaches:
def security_model_comparison():
“”“
Each approach makes different trade-offs
“”“
models = {
‘HD_Wallet’: {
‘security’: ‘Single point of failure (seed)’,
‘recovery’: ‘Seed phrase only’,
‘flexibility’: ‘None’,
‘complexity’: ‘Low’,
‘cost’: ‘Free deployment’
},
‘MPC_Wallet’: {
‘security’: ‘Distributed (no single point)’,
‘recovery’: ‘Share refresh/regeneration’,
‘flexibility’: ‘Limited to threshold schemes’,
‘complexity’: ‘High (coordination required)’,
‘cost’: ‘Infrastructure costs’
},
‘Smart_Wallet’: {
‘security’: ‘Programmable policies’,
‘recovery’: ‘Social/time-locked/custom’,
‘flexibility’: ‘Unlimited’,
‘complexity’: ‘High (smart contract risk)’,
‘cost’: ‘Deployment + transaction overhead’
}
}
# The key insight: They’re not mutually exclusive
# Hybrid approaches are emergingThe Hybrid Future
The most interesting developments combine multiple approaches:
def hybrid_wallet_architecture():
“”“
Combining MPC + Smart Contracts + Passkeys
“”“
class HybridWallet:
def __init__(self):
# MPC for key security
self.mpc_shares = distribute_key_shares(n=5, threshold=3)
# Smart contract for programmable logic
self.contract = deploy_smart_wallet()
# Passkeys for user authentication
self.passkey = register_webauthn_credential()
def execute_transaction(self, tx):
# User authenticates with passkey
passkey_sig = self.passkey.sign(tx)
# MPC nodes verify and create partial signatures
partial_sigs = []
for share in self.mpc_shares[:3]:
if share.verify_passkey(passkey_sig):
partial_sigs.append(share.partial_sign(tx))
# Combine into threshold signature
final_sig = combine_signatures(partial_sigs)
# Smart contract validates and executes
self.contract.execute(tx, final_sig)This architecture provides defense in depth through multiple security layers that must all be compromised for an attack to succeed.
Philosophical Questions
As I’ve worked with smart wallets, several philosophical questions emerge:
Are we over-engineering? Simple EOAs with hardware wallets have protected billions in value. Do most users need programmable wallets, or are we creating complexity that will lead to new failure modes?
Who controls the code? If your wallet’s security depends on smart contract code, who wrote that code? Who audited it? Can you understand it? We’re replacing “not your keys, not your coins” with “not your code, not your coins.”
Is determinism desirable? Smart wallets often use deterministic addresses (CREATE2), but this reveals your address before deployment. Anyone can pre-compute where your wallet will be and monitor it.
What about quantum resistance? Smart wallets can upgrade their signature schemes, but this requires maintaining pre-quantum access. If quantum computers arrive suddenly, upgrade windows might be too short.
Principles of Smart Contract Wallets
Smart contract wallets represent a fundamental shift from protecting secrets to programming security. They offer capabilities impossible with traditional wallets: gasless transactions, social recovery, spending limits, automated strategies, and seamless upgrades.
Yet they also introduce new complexities: deployment costs, bundler dependencies, upgrade risks, and smart contract vulnerabilities. The technology is powerful but not mature and we’re still discovering failure modes and best practices.
The experiments I’ve been running suggest a few principles:
Start simple, add complexity gradually - Don’t implement every feature immediately
Separate concerns - Key management, policy logic, and execution should be modular
Plan for failure - Include escape hatches and recovery mechanisms
Audit everything - Smart contract bugs are permanent and public
Educate users - Programmable security requires understanding the programs
In the next part of this series, we’ll explore how these different approaches - HD wallets, MPC, and smart contracts, are beginning to converge into unified architectures that might finally solve crypto’s usability-security paradox.
The wallet signing transactions while I sleep has executed 237 operations this month, saved me approximately $89 in optimized gas fees, and automatically rebalanced my portfolio twice. It’s not perfect; I’ve had to manually intervene three times when edge cases exceeded its programmed logic. But it represents something profound: wallets that aren’t just containers for keys, but active participants in our financial lives.
We’re moving from wallets that hold secrets to wallets that hold strategies. The question isn’t whether this is the future; it’s how we get there safely.